
In the rapidly evolving world of technology, businesses rely heavily on software systems to streamline operations, enhance productivity, and drive growth. However, the complex nature of software development and the constant emergence of new threats make it essential for organizations to conduct regular software audits.
What is a Software Audit?
A software audit service evaluates an organization's software systems to ensure compliance, licensings, and security. It involves reviewing documentation, conducting interviews, analyzing code, and performing security testing.
The service helps identify non-compliant software, unauthorized installations, and security risks. It provides recommendations for remediation, optimizations licensing, and enhancing security.
Overall, software audit services ensure compliance, optimize software usage, and maintain a secure environment.
Benefits of Software Audits
- Identifying Vulnerabilities: One of the key benefits of a software audit is the ability to identify vulnerabilities and weaknesses in the software infrastructure. By thoroughly examining the software code, configuration, and architecture, organizations can uncover security gaps and address them proactively.
- Ensuring Compliance: Software audits help organizations ensure compliance with industry regulations and standards. By reviewing software licenses, usage, and distribution, businesses can ensure that they are operating within legal boundaries and avoiding potential penalties or legal issues.
- Enhancing Performance: Through a software audit, organizations can identify performance bottlenecks and optimize their software systems for better efficiency. This can result in improved user experience, reduced downtime, and increased overall productivity.
- Safeguarding Intellectual Property: Software audits play a vital role in protecting intellectual property rights. By verifying the authenticity of software licenses and ensuring that proprietary code is secure, organizations can safeguard their valuable assets from unauthorized use or theft.
How Does a Software Audit Work?
A software audit typically involves several steps:
1. Planning: The audit process begins with planning, where the scope and objectives of the audit are defined. This includes identifying the software systems to be audited and gathering necessary documentation.
2. Data Collection: The auditor collects data related to software installations, licenses, usage, and security measures. This can involve reviewing documentation, conducting interviews with relevant personnel, and using specialized tools to gather data.
3. Analysis: The collected data is then analyzed to identify any discrepancies, noncompliant software usage, unauthorized installations, or security vulnerabilities. The auditor examines license agreements, compares installations with licenses, and assesses security controls.
4. Reporting: The findings of the audit are documented in a comprehensive report. This report includes an overview of the audited systems, identified issues, and recommendations for remediation. It may also include insights on optimizing software usage, enhancing security measures, and ensuring compliance.
5. Remediation: Based on the audit findings, the organization takes necessary actions to address any identified issues. This may involve acquiring proper licenses, removing unauthorized software, implementing security measures, and updating software configurations.
6. Follow-up: After remediation, a follow-up review may be conducted to ensure that the identified issues have been resolved and that the necessary actions have been implemented.
The Importance of Software Audits
Software audits are crucial for several reasons:
Security: With the rising number of cyber threats, software audits are essential for maintaining a robust security posture. Regular audits help identify and mitigate potential risks, ensuring the confidentiality, integrity, and availability of data and systems.
Compliance: Many industries have strict regulations regarding data privacy and security. Software audits help organizations ensure compliance with these regulations, avoiding costly penalties and reputational damage.
Cost Savings: By uncovering inefficiencies and optimizing software systems, audits can result in significant cost savings. Identifying and addressing vulnerabilities early on prevents potential security breaches and the associated financial losses.
Types of Software Audits
There are several types of software audits, including:
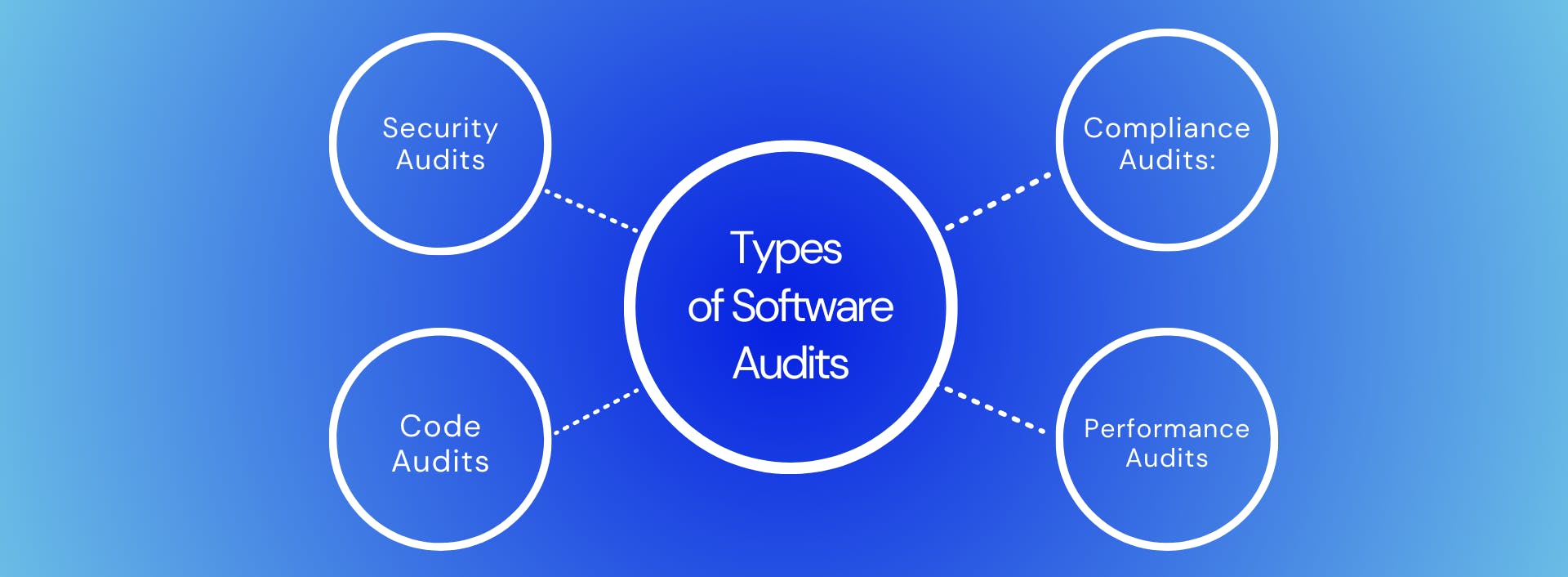
Security Audits: Focus on identifying vulnerabilities and weaknesses in software systems to mitigate security risks.
Compliance Audits: Ensure that software usage aligns with licensing agreements and industry regulations.
Code Audits: Examine the quality and security of software code to identify coding errors, potential vulnerabilities, and adherence to coding best practices.
Performance Audits: Assess the performance and scalability of software systems to optimize efficiency and user experience.
Case Study - ERC20 Smart contract for decentralized cryptocurrency exchange
Our team performed an analysis of code functionality, manual audits, and automated checks with Mythril and Slither. All issues found during automated analysis were manually reviewed, and important vulnerabilities were presented in the Audit Overview.
How we made it?
This project was handled by specialists in Solidity with knowledge of Ethereum Blockchain and competitive solutions. First, we performed an analysis of code functionality, manual audit, and automated checks with Mythril and Slither. All issues found during automated analysis were manually reviewed, and important vulnerabilities were presented in the Audit Overview. We conducted a Smart Contract Code Review and Security Analysis for the client. This included Architecture Review, Functional Testing, Computer-Aided Verification, and Manual Review.
According to audit results and client requirements, the team selected appropriate tools to develop the system. Our specialist created a smart contract prepared for implementation on the blockchain BSC (Binance Smart Chain). The solution was implemented in the client's application.
What is the final effect for the client?
We have created a solution that provides fast and secure transactions using virtual currency. Our system uses blockchain technology to equitably distribute new cryptocurrencies regardless of investor capital. When users sign a smart contract to transfer money, the funds will be sent over the Ethereum network, and register the transaction on the ETH blockchain as immutable public data.
What were the benefits?
The created system is designed to be highly resistant to modification and fraud. Our solution ensures a high level of security, performance stability, and efficiency.
In this project, the BCF team has successfully demonstrated their skills, expertise, and excellence in software development.
Contact us today to find out how we can help your company achieve great success!


